
Bitwarden CLI hack, arrest of illicit debt collectors in Kyiv, and other cybersecurity news
The week's key cybersecurity stories: AI-fuelled DPRK heists, Bitwarden CLI breach, spyware spread.
We have compiled the week’s most important cybersecurity news.
- North Korean hackers stole $12m in crypto in three months using AI tools.
- A former ransomware negotiator turned out to be an accomplice.
- UK intelligence: 100 governments have access to commercial spyware.
- An infostealer was planted in Bitwarden’s developer-facing password manager.
North Korean hackers stole $12m in crypto in three months using AI tools
Over three months, the North Korean hacking group HexagonalRodent stole about $12m in cryptocurrency and infected more than 2,000 Web3 developers’ machines to steal credentials and gain access to crypto wallets, said Expel cybersecurity specialist Marcus Hutchins.
The campaign relied on “vibe coding” — generating malware and infrastructure via text prompts to AI systems:
- using Anima’s AI web-design tools, the hackers built sites for non-existent IT firms;
- victims were lured with fake job listings and asked to complete a “test assignment” that contained malware;
- all code and correspondence in flawless English were generated with ChatGPT and Cursor.
The expert analysed the hackers’ infrastructure, which they inadvertently left exposed. Their prompts and a database of victims’ wallets leaked online. Hutchins noted the code was filled with English comments and emojis — a clear sign the software was entirely generated by a LLM.
Hutchins argues that in 2026 Pyongyang made a qualitative leap by using AI to automate every stage of its cyberattacks, turning low-skilled operators into a scaled cyberthreat.
HexagonalRodent’s work is only part of North Korea’s broader strategy to automate crime, corroborated by reports from other technology firms:
- Microsoft reported that North Korean operators use AI to generate fake documents, research vulnerabilities and conduct social engineering;
- Anthropic said it blocked attempts by DPRK agents to use the Claude model to refine malware.
In comments to WIRED, representatives of OpenAI, Cursor and Anima confirmed misuse of their services. They said accounts linked to the hackers had been blocked; the investigation will help prevent similar incidents.
A former ransomware negotiator turned out to be an accomplice
Angelo Martino, formerly a ransomware negotiator at cybersecurity firm DigitalMint, pleaded guilty to aiding cybercriminals, the US Department of Justice said.
Martino admitted he played both sides in five separate incidents. While ostensibly working for victims, he passed confidential information to operators of the ALPHV/BlackCat malware and supplied details such as insurance coverage limits and victims’ negotiation strategies.
Investigators found that Martino maximised the payouts to criminals and took a cut.
The ALPHV/BlackCat group operated a CaaS model, in which the gang builds and maintains file-encrypting software while “affiliates” deploy it in attacks and share profits with the developers.
In 2023, law enforcement seized the gang’s dark-web site and released a decryptor that helped more than 500 victims restore systems.
In 2025, other DigitalMint employees — Kevin Tyler Martin and Ryan Clifford Goldberg — aided the same criminals. Together with Martino they earned over $1.2m from just one victim.
Martino pleaded guilty to extortion and faces up to 20 years in prison. Authorities seized $10m in assets from him.
UK intelligence: 100 governments have access to commercial spyware
According to British intelligence, more than half of the world’s governments have access to software capable of hacking devices to steal confidential information, Politico reports.
Media say the barrier to obtaining such surveillance technology has fallen. The number of countries potentially possessing these hacking tools has risen to 100, up from 80 known in 2023.
Commercial spyware developed by private firms — such as Pegasus from NSO Group — often relies on vulnerabilities in phone and computer software. Governments say these tools are used only on devices of suspects in serious crimes, including terrorism.
In recent years, the “circle of victims” has widened from political critics, opponents and journalists to bankers and wealthy businesspeople, according to UK intelligence.
In the US, ICE is actively using the Israeli-made Graphite tool. Acting agency director Todd Lyons confirmed this to NPR.
According to him, law enforcement uses the software to fight foreign terrorist organisations and fentanyl traffickers who rely on encrypted messengers. The tool can access messages on a phone without any need to click links (zero-click).
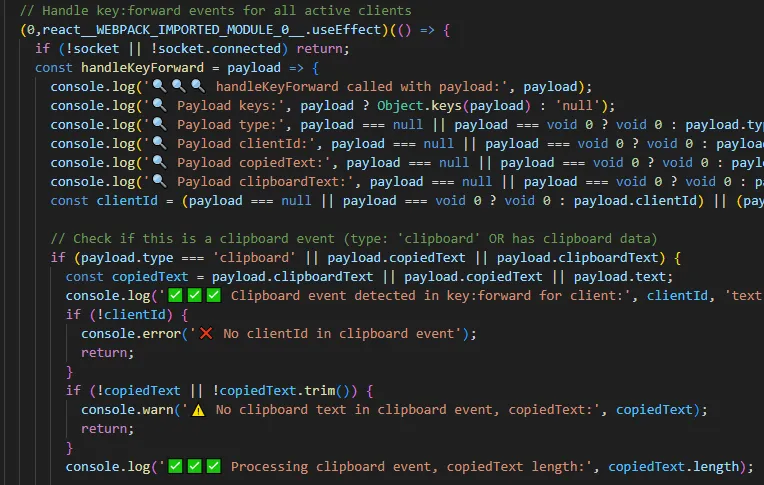
An infostealer was planted in Bitwarden’s developer CLI
On 22 April 2026, the official npm package of the Bitwarden command-line interface (CLI), version 2026.4.0, was compromised. The repository contained a build with malicious code to steal developers’ credentials.
Several security firms analysed the supply-chain compromise and assessed the incident:
- JFrog experts found the package used a custom loader, bw_setup.js, to stealthily execute a spying script. The malware collected npm and GitHub tokens, SSH keys, and credentials for AWS, Azure and Google Cloud;
- OX Security discovered that the encrypted stolen data were exfiltrated by automatically creating public repositories on the victim’s GitHub account. The repos were tagged “Shai-Hulud: The Third Coming,” and the malware could self-propagate;
- Socket confirmed the malware targeted CI/CD infrastructure. It also found technical links to the recent supply-chain compromise at Checkmarx.
The attack is attributed to the TeamPCP group, previously behind large campaigns against developers of Trivy and LiteLLM. Experts strongly urged developers to rotate all keys and tokens immediately if they interacted with the affected CLI.
Bitwarden removed the tainted version just 90 minutes after the attack began and confirmed that user vaults and passwords remained safe.
Apple fixed a bug that let the FBI read deleted Signal notifications
Apple released a patch and a security advisory after the FBI gained access to Signal message notification content via iOS even after the app had been deleted.
We are very happy that today Apple issued a patch and a security advisory. This comes following @404mediaco reporting that the FBI accessed Signal message notification content via iOS despite the app being deleted.
Apple’s advisory confirmed that the bugs that allowed this to…
— Signal (@signalapp) April 22, 2026
Signal said that once the update is installed, all inadvertently saved notifications will be deleted and new ones will not be stored.
Kyiv police detained a gang of debt collectors who extorted cryptocurrency using bot farms
In Kyiv, law enforcement detained fraudsters who used the Bitcapital and Crypsee platforms to provide crypto loans. Debtors and their relatives were harassed with AI-generated abusive content and a bot farm with 6,000 SIM cards, the Cyber Police of Ukraine reported.
According to investigators, the group set up a call centre in Dnipro and had operated since 2023 under cover of companies registered in the UK and Cyprus.
Operators phoned debtors and, using fake data and voice-changing software, demanded repayment. Even when clients repaid on time, the criminals invented non-existent debts. They then extorted money through threats and blackmail.
The bot farm was used to generate and disseminate degrading content featuring victims’ data and photos — as well as those of their relatives and colleagues — and to place systematic threatening phone calls.

At any one time, a separate group of two to six people could “work” a victim, tailoring approaches to individual vulnerabilities. On success, each took a cut of the funds extorted.
Police carried out 44 searches in Dnipropetrovsk region and Kyiv. More than 80 mobile phones, computer equipment, cash, documents, seals and bot farms were seized.
Preliminary damages exceed 5m hryvnia (about $113,000 at the time of writing). The suspects face up to 12 years in prison.
Also on ForkLog:
- Tether froze $344m in USDT at the request of the US.
- In the UK, raids were conducted to crack down on illicit P2P crypto trading.
- Cybersecurity experts warned of a new wave of DPRK attacks.
- Bloomberg reported unauthorised access to the Mythos AI model.
- Hackers attacked Volo and drained $3.5m from WBTC and USDC pools.
- Reporters learned of a new scheme to extort bitcoin for passage through the Strait of Hormuz.
- Arbitrum froze 30,000 ETH as part of the Kelp hack investigation.
- Eth.limo regained control of its domain after the easyDNS breach.
- The Kelp protocol lost $293m after a cross-chain bridge attack.
What to read this weekend?
For a long time, the use of cyberweapons for espionage was seen as the domain of a narrow circle of intelligence services. But a US investigation into Operation Zero exposed the scale of trading in zero-day vulnerabilities.
On states’ shadow markets and the price of hacks — in ForkLog’s new feature.
Рассылки ForkLog: держите руку на пульсе биткоин-индустрии!


