
CertiK Reports on North Korea’s ‘Industrialization’ of Crypto Theft
North Korean hackers industrialize crypto theft, says CertiK.
Hacker groups linked to North Korea have turned cryptocurrency theft into a large-scale state operation with their own money laundering infrastructure and a network of IT agents, according to analysts at CertiK.
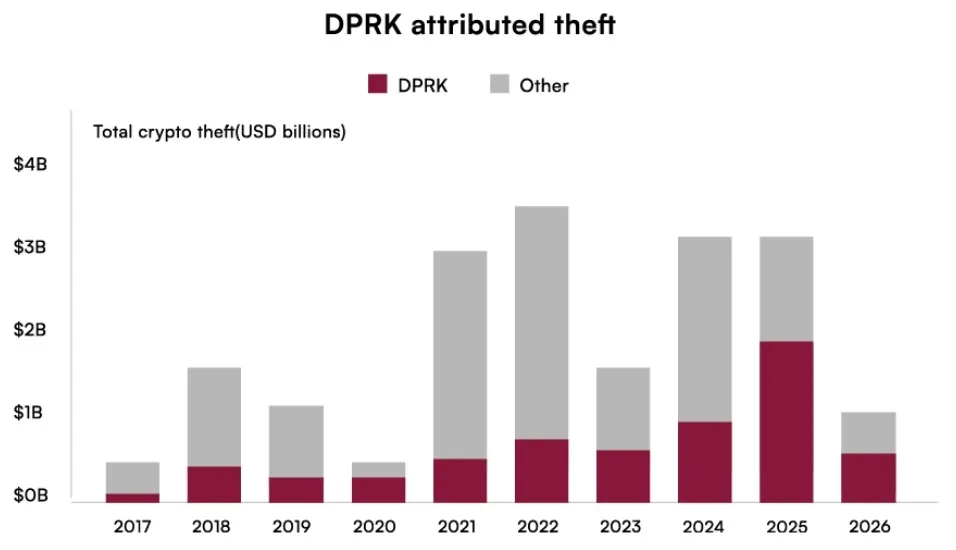
DPRK-linked actors have stolen an estimated $6.75B across 263 crypto incidents since 2016.
In 2025 alone, they accounted for 60% of all stolen value despite just 12% of incidents.
Read our full Skynet DPRK Crypto Threats Report below 👇https://t.co/06QCTVvi0E
— CertiK (@CertiK) May 12, 2026
Researchers estimate that from 2017 to early 2026, North Korean entities stole digital assets worth more than $6.7 billion in 263 incidents. The scale of losses is likely understated, as it does not account for “hundreds of small attacks” on individuals and projects in the early years of the crypto industry.
In 2025 alone, Pyongyang-backed entities inflicted $2.06 billion in damage on the industry, accounting for approximately 60% of the total figure, despite being responsible for only 12% of incidents.
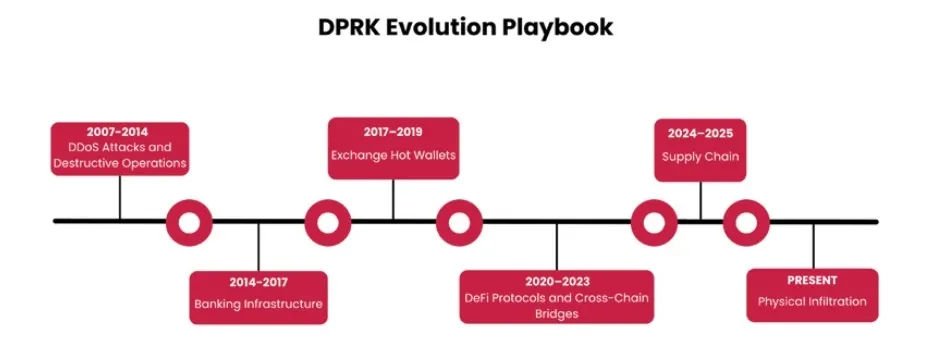
Changes in Tactics
CertiK stated that North Korean groups have shifted from “chaotic attacks” to professionalized operations with clear role divisions. Some divisions focus on social engineering, while others compromise infrastructure. Money laundering is also handled by specialized personnel.
Analysts identified periods when hackers in the industry concentrated on specific attack vectors:
- Hot wallets of crypto exchanges (2017-2019) — insufficient development of storage security systems required fewer resources for operations (cases like Bithumb, Coincheck, and others).
- DeFi protocols and cross-chain bridges (2020-2023) — became relatively accessible targets as centralized platforms strengthened cyber defenses. Examples: Ronin Bridge and Harmony Horizon.
- Supply chains (2024-2026) — instead of directly attacking crypto exchanges, attackers shifted to compromising third-party infrastructure providers. The most notable case: theft of $1.5 billion in cryptocurrency from Bybit through a product hack from Safe.
- Physical penetration (since 2025) — attacks began to combine social engineering methods, infiltration of IT agents into crypto companies, contacts with projects as fake venture investors, and technical methods. Example: Drift Protocol with a loss of $280 million.
Asset Laundering
After the largest Bybit hack of $1.5 billion, attributed to the Lazarus group, about 86% of the stolen Ethereum funds were converted into Bitcoin in less than a month.
To obscure the trail, the following were used:
- rapid transfers of assets between different blockchains (chain hopping);
- cross-chain bridges;
- crypto mixers;
- over-the-counter brokers;
- underground banking networks in Asia.
Analysts emphasized that the money laundering infrastructure has become “as important as the attacks themselves” for the hackers.
‘Army of IT Workers’
Researchers identified a separate threat from North Korean IT specialists who pose as remote employees to infiltrate Western companies.
These agents can:
- gain access to internal systems;
- participate in code development;
- embed malicious components;
- gather data for future attacks.
In some cases, AI tools and deepfake technologies were used to pass interviews.
The North Korean Foreign Ministry denied accusations of the country’s involvement in cryptocurrency thefts, calling such claims “absurd slander” and a “political tool” of the United States.
Рассылки ForkLog: держите руку на пульсе биткоин-индустрии!


