The widespread use of digital assistants poses critical risks: users become vulnerable to data leaks, hacks, and cryptocurrency theft. This warning comes from specialists at CertiK.
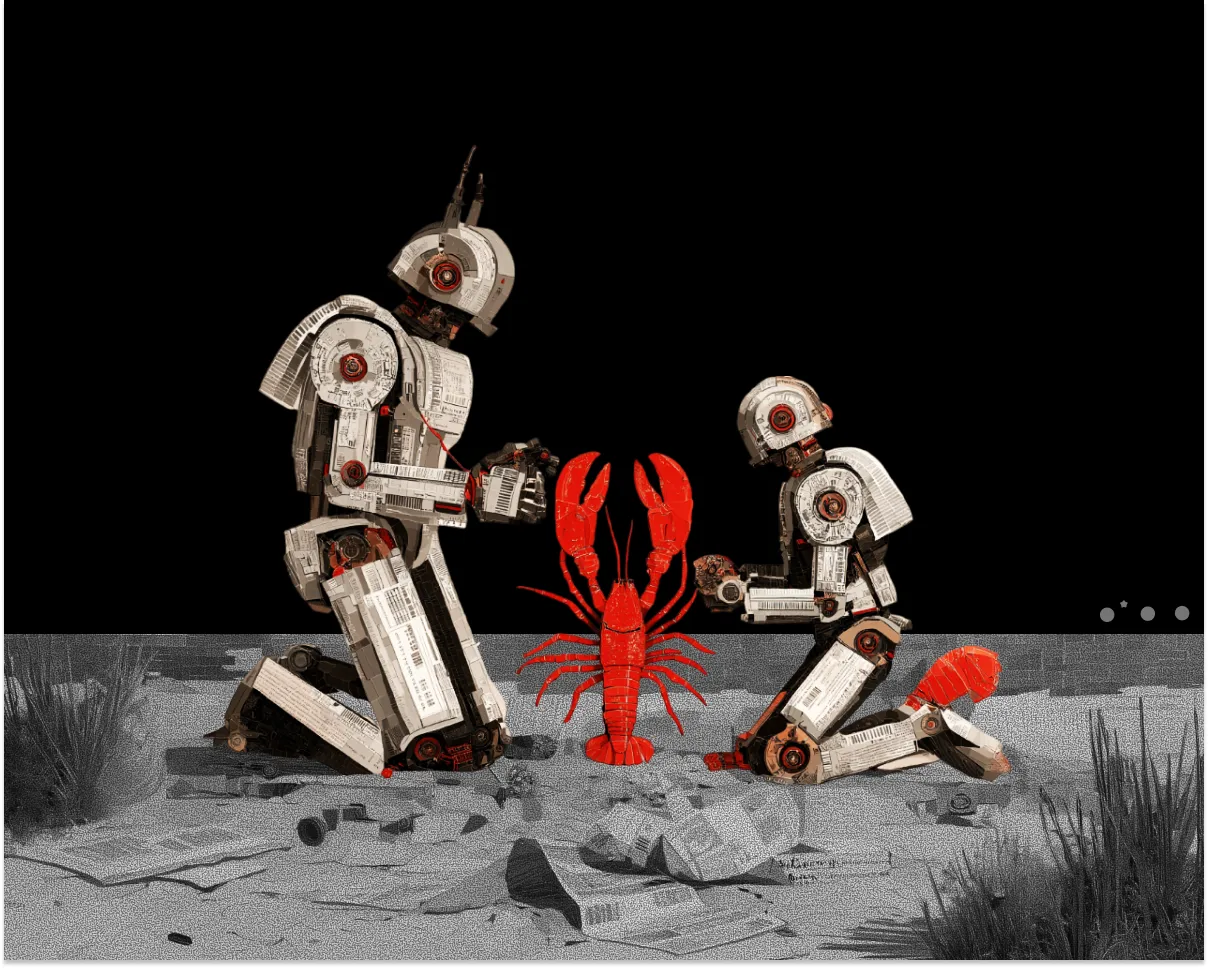
What happens when an AI agent gets broad access before security catches up?
Our latest report examines OpenClaw’s attack surface, from gateway takeover and identity bypass to prompt injection and supply chain risk.
Read the full report👇https://t.co/x0RfYYic0T
— CertiK (@CertiK) March 31, 2026
According to them, OpenClaw has become the “leading vector for global software supply chain attacks.”
The AI agent acts as a bridge between external data and local execution, “opening standard channels for attacks.” One such channel is the interception of the local gateway.
Malicious websites or scripts exploit the assistant’s presence on a device to steal confidential data or perform unauthorized actions.
Particular danger also comes from OpenClaw plugins and malicious skills, which can be installed from local sources or marketplaces.
Unlike traditional viruses, they can manipulate the agent’s behavior through natural language, making them resistant to ordinary scanning. Once launched, such software can extract sensitive information, including cryptocurrency wallet credentials.
CertiK emphasized that infected components hide within legitimate codebases and download seemingly ordinary URLs. These links ultimately deliver shell commands or malicious scripts.
Extensive Network and Recommendations
Malefactors have deliberately placed malicious skills in various high-value categories: utilities for Phantom, address trackers, tools for finding “insider” wallets, Polymarket tools, and Google Workspace integrations.
“They have covered an incredibly wide range of the crypto ecosystem, targeting mass infection of browser extension wallets: MetaMask, Phantom, Trust Wallet, Coinbase Wallet, OKX Wallet, and many others,” the experts added.
Researchers also noted that the fraudsters’ actions resemble familiar methods in the digital asset sector. These include social engineering, deception through fake utilities, credential theft, and phishing.
CertiK advised ordinary users—not security experts, developers, or geeks—not to install OpenClaw and to wait for “more mature, secure, and manageable versions.”
OpenClaw Issues
OpenClaw emerged as a byproduct of Clawdbot, launched in November 2025. The project quickly gained popularity among developers and users. The number of stars on GitHub exceeded 340,000.
In March, a wave of excitement over the AI agent swept China: nearly 1,000 people lined up at Tencent headquarters to install OpenClaw on their computers. However, the country’s Cyber Center soon warned of the platform’s associated risks, leading to the emergence of a paid service for removing the AI agent in China.
Many independent experts also raised questions about the software’s security. Just weeks after its release, Bitsight specialists discovered 30,000 versions of OpenClaw available for free.
SecurityScorecard researchers found 135,000 copies in 82 countries, of which 15,200 were vulnerable to remote code execution, CertiK noted.
The digital assistant has become “the most scrutinized platform in terms of security.” The project has accumulated over 280 GitHub Security Advisories, 100 vulnerabilities (CVE), and “a series of ecosystem-level attacks.”
Back in March, the cybersecurity company OX Security had already reported that malefactors were exploiting OpenClaw’s popularity to conduct phishing campaigns and steal cryptocurrencies from developers.