
Cyberattacks surge amid Middle East escalation, leaked iPhone spyware, and other cybersecurity news
Weekly digest: Middle East cyberattacks, iPhone spyware leak, FBI forum takedown.
We gathered the week’s most consequential cybersecurity news.
- The Middle East conflict sparked cyberattacks across 16 countries.
- Kazakhstan suspects a group of laundering $4.7 million via cryptocurrency.
- Researchers uncovered spyware tools for hacking iPhones.
- The FBI shut down a cyber forum with data on 142,000 members.
Middle East conflict sparked cyberattacks across 16 countries
Cybersecurity researchers at Radware warned of a spike in hacker activity following a coordinated military campaign by the US and Israel against Iran.
The first DDoS attacks were recorded on 28 February. Analysts said the operation was carried out by Hider Nex (also known as Tunisian Maskers Cyber Force), a Tunisian hacktivist group. It uses a “hack-and-leak” strategy, combining deliberate network overloads with data theft to push its agenda.
According to Radware, between 28 February and 2 March there were 149 claims of denial-of-service attacks targeting 110 organisations in 16 countries. Twelve different groups took part, with Keymous+ and DieNet accounting for roughly 70% of all activity.
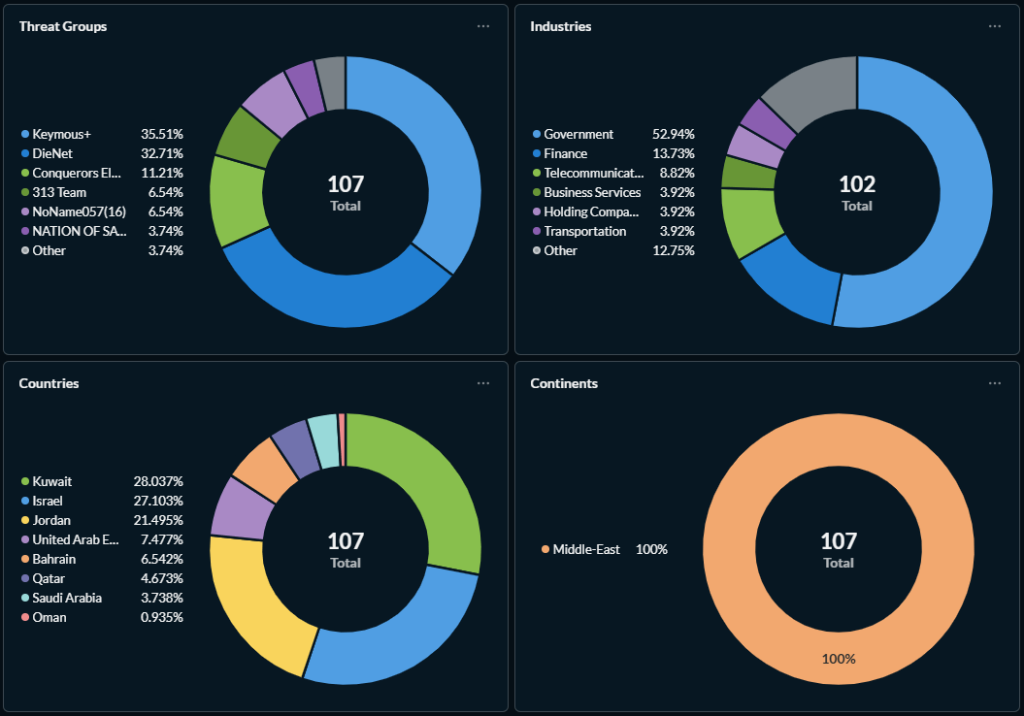
Attack statistics:
- the vast majority of attacks (107) were concentrated in the Middle East. Europe accounted for 22.8% of global activity;
- almost 47.8% of affected organisations were in the public sector, followed by finance (11.9%) and telecommunications (6.7%);
- within the Middle East, attacks hit Kuwait (28%), Israel (27.1%) and Jordan (21.5%).
Other groups involved included Nation of Saviors, Conquerors Electronic Army, Sylhet Gang, 313 Team, Handala Hack, APT Iran and others.
According to The Hacker News, the current wave of cyberattacks includes:
- breaches of military networks. Pro-Russian Cardinal and Russian Legion claimed to have hacked Israeli military networks, including the “Iron Dome” air-defence system;
- SMS phishing. One target was the RedAlert app — the mobile version of the “Tzeva Adom” (“Red Color”) early-warning system. The attackers likely exploited vulnerabilities to implant spyware on devices;
- the revival of old threats. The Cotton Sandstorm (Haywire Kitten) group resurfaced as Altoufan Team, attacking websites in Bahrain.
Kazakhstan suspects group of laundering $4.7m via cryptocurrency
Kazakh law enforcement detained suspects accused of illegal activity and money laundering using cryptocurrency, the press service of the AFM reported.
Investigators said the organiser ran a scheme to profit from transactions in digital assets. Participants recruited “droppers,” registered bank cards and exchange accounts in their names, conducted financial operations and then cashed out the proceeds.
Money sent to bank cards of more than 150 intermediaries was transferred to their crypto wallets on the ATAIX exchange. The criminals provided fake loan agreements between account holders and an affiliated legal entity, after which the funds were converted into digital assets and sent to OKX addresses.
For conversion and withdrawal, a controlled exchange point was used to move funds into foreign currency. The total value of transactions exceeded 3.5 billion tenge (about $4.7 million at the time of writing).
During searches, officers seized 46 mobile phones, 92 bank cards and 25,463 USDT.
Researchers uncovered spyware tools to hack iPhones
Cybersecurity researchers at Google Threat Intelligence Group (GTIG) found a powerful toolkit for hacking iPhones running older iOS versions. They believe criminals obtained the spyware following a leak from a government customer.
The exploit bundle, dubbed Coruna, was first detected by Google in February 2025 during an attempt by a surveillance-technology vendor to hack a phone with spyware on behalf of a government agency.
Months later, the malware was spotted in a large-scale campaign by a Russian espionage group against Ukrainian users, and later with a hacker in China.
Google researchers warned of an emerging market for “second-hand” exploits, resold to hackers seeking to maximise returns on vulnerabilities.
Mobile-security firm iVerify reverse-engineered the tools. Its specialists linked the Coruna package to the US government, based on similarities to software previously attributed to the United States.
According to Google’s experts, Coruna is highly dangerous: it can bypass iPhone protections via a simple visit to a malicious website (for example, by following a link), a technique known as a “watering hole” attack. The package can compromise a handset in five different ways, chaining 23 distinct vulnerabilities. Devices running iOS versions from 13 through 17.2.1 remain at risk.
FBI shut down cyber forum with data on 142,000 members
In a Europol-led operation, the FBI seized a major online platform used by hackers to trade intrusion tools and stolen data.
On 3–4 March, law enforcement blocked two LeakBase domains and warned users that evidence was being collected. Simultaneously, searches, arrests and interviews took place in the US, Australia, Belgium, Poland, Portugal, Romania, Spain and the UK.
LeakBase had operated since 2021 and was initially backed by the ARES hacking group. It grew substantially after the Breached forum was shut down — its audience exceeded 142,000 members.
Registration was free. The forum offered access to databases, a marketplace for leaks and exploits, an escrow payment system, and sections on programming, social engineering and cryptography.
Alabama resident blackmailed hundreds of women after hacking their accounts
A 22-year-old Alabama man pleaded guilty to extortion, cyberstalking and fraud after hacking the social-media accounts of hundreds of women, the US Department of Justice said.
From April 2022 to May 2025, Jamarcus Mosley posed as victims’ friends and used other manipulation tactics to trick women into handing over recovery codes and passwords. He then seized control of their Snapchat, Instagram and other social-media accounts.
After the hacks, he threatened to publish private intimate photos and videos or permanently block access unless his demands were met:
- granting full access to additional accounts;
- sending new sexualised content;
- paying various sums of money.
Prosecutors said that in one case Mosley used a hacked account belonging to a 17-year-old victim to contact her 13-year-old sister. He sent her a Snapchat map screenshot, implying he knew where she lived. In another case he posted stolen images of a victim online.
Also on ForkLog:
- A hacker withdrew $2.7m from Solv Protocol amid an unexpected token surge.
- US authorities arrested a suspect in the theft of $46m from a government wallet.
- Microsoft and Coinbase helped shut down the Tycoon phishing service.
- Hackers targeted crypto specialists while posing as venture investors.
- An app appeared online to detect smart glasses.
- Errors were found in OpenAI’s AI benchmark for auditing blockchains.
- A court dismissed fraud claims against Uniswap.
- Crypto-market losses from hacks fell to an 11-month low.
- Tether has frozen $4.2bn in illicit funds to date.
What to read this weekend?
In a new ForkLog feature, Krzysztof Szpak examines how AI street-surveillance systems work in big cities and why governments rushed to roll them out everywhere.
Рассылки ForkLog: держите руку на пульсе биткоин-индустрии!


