
Ethereum Address Spoofing Attacks Surge by 600% Following Fusaka Update
Address poisoning in Ethereum surges 600% post-Fusaka, with "dust" transfers rising sharply.
The practice of address poisoning in the Ethereum network is becoming widespread. Following the Fusaka update, the number of “dust” transfers of USDT increased by 612%, according to Etherscan data.
— etherscan.eth (@etherscan) March 12, 2026
The reduction in network fees due to the upgrade has triggered a new wave of fraudulent activity. Malefactors are sending millions of zero-value microtransactions to clutter the transaction history in victims’ wallets.
Their main goal is to trick users into mistakenly copying a fake address from the list of recent transactions.
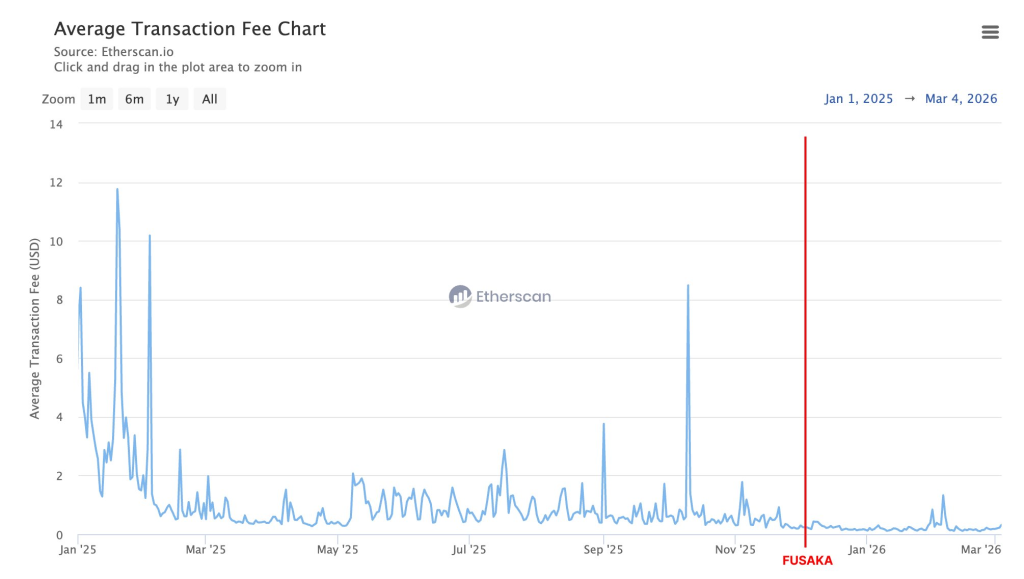
In the 90 days following the activation of the update on December 3, 2025, the number of “dust” transfers—transactions of less than $0.01—soared compared to the same period before the upgrade:
- USDT: +612% (from 4.2 million to 29.9 million);
- USDC: +473% (from 2.6 million to 14.9 million);
- DAI: +470% (from 142,000 to 811,000);
- ETH: +62% (from 104.5 million to 169.7 million).
Meanwhile, the number of regular transactions over $0.01 remained unchanged, indicating a spike in fraudulent activity rather than organic network growth.
How It Works
Fraudsters monitor large transfers on the blockchain. Automated systems generate lookalike addresses that mimic the first and last characters of addresses with which the victim recently interacted.
Then, scammers send “dust” transfers to ensure the fake address appears in the transaction history. They hope the victim will copy the counterfeit details and send funds to it.
Sometimes, several hacker groups compete to “poison” a wallet. One Etherscan screenshot shows up to 13 fake transactions from different attackers entering a victim’s history within minutes of a legitimate USDT transfer.
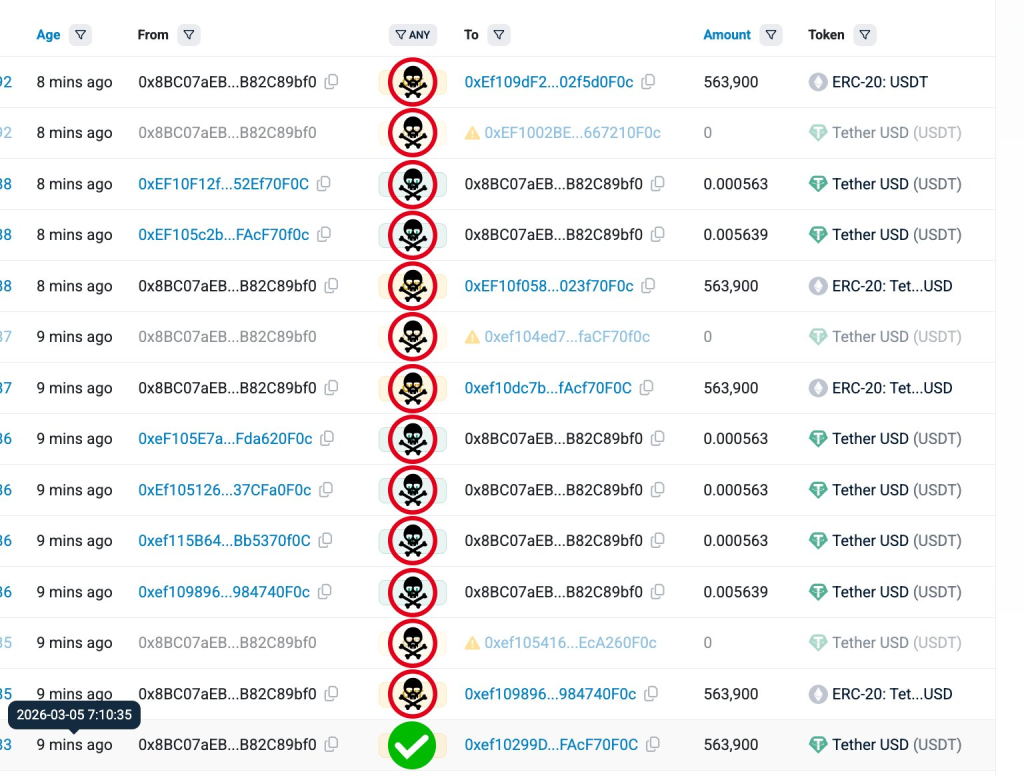
Analysts also mentioned a complaint from a user named Nima. He reported receiving over 89 alert emails about address activity after two stablecoin transfers.
Address poisoning attacks are getting out of hand. I just sent two stablecoin transactions and received +89 emails from my Etherscan address watch alert notifications.
It took them <30 mins to create all of these on mainnet. So many will fall victim to this. pic.twitter.com/H1nGaMMprE
— Nima 👁️ (@0xNimaRa) February 13, 2026
The Scale of the Problem
From July 2022 to June 2024, experts from Blockchain Address Poisoning recorded around 17 million attempts to deceive users through address spoofing. Approximately 1.3 million people were targeted, with total damages exceeding $79 million.
The issue is more acute in networks with low fees. For instance, on Binance Smart Chain, the number of fake transfers is 1355% higher than in Ethereum.
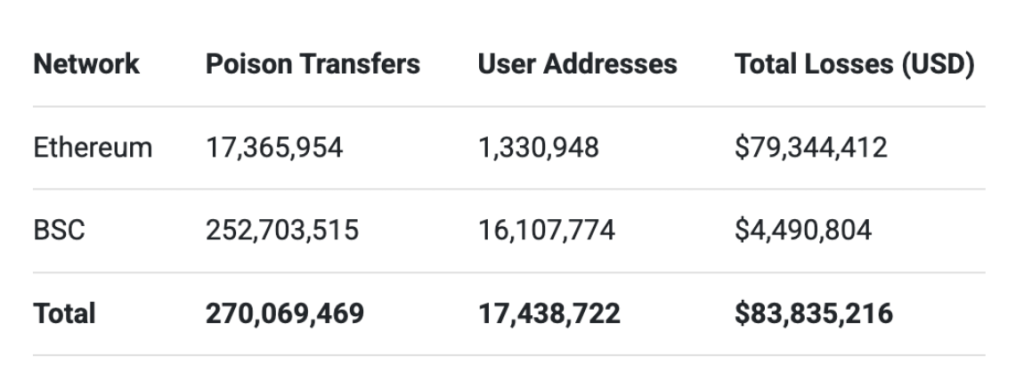
Only a small fraction of attacks—about 0.01%—are successful. However, the sheer volume of these campaigns makes the scheme highly profitable.
“Instead of targeting individual addresses, campaigns often send thousands or even millions of fake transfers. With enough attempts, even a tiny success rate can yield significant profits,” noted Etherscan.
Back in December 2025, an investor lost nearly $50 million due to an address spoofing attack. Binance founder Changpeng Zhao proposed additional security measures to “eradicate” this practice.
Рассылки ForkLog: держите руку на пульсе биткоин-индустрии!


