Google Uncovers DarkSword Exploit Chain Targeting iPhones
Google experts uncover DarkSword, an iOS exploit chain targeting crypto wallets.
Google experts have identified a complex exploit chain for iOS known as DarkSword. The Ghostblade tool within its structure is designed to steal confidential information, including cryptocurrency wallet data.
Google Threat Intelligence has exposed “DarkSword”, a full-chain iOS exploit using 6 vulnerabilities to silently compromise iPhones.
Your seed phrases and wallet credentials are a target.
🧵 Here’s what you need to know 👇
— CertiK Alert (@CertiKAlert) March 20, 2026
What Happened
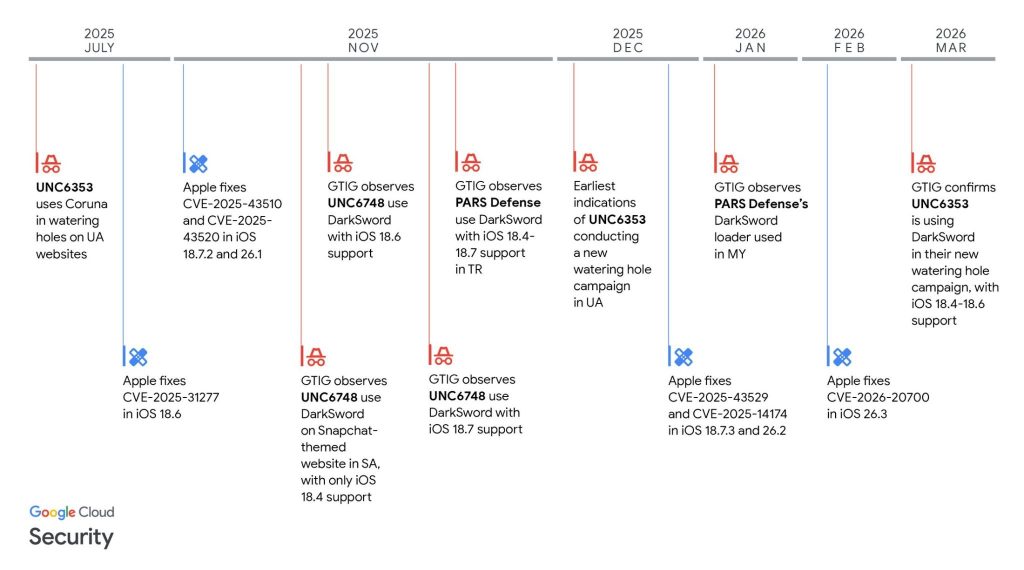
Specialists from Google’s Threat Intelligence Group have discovered a so-called full-chain exploit, combining multiple vulnerabilities in the iOS operating system, allowing for the complete compromise of Apple devices. The software package has been used by several hacker groups and commercial spyware providers.
Attacks were conducted through malicious websites: upon visiting, the device would trigger an exploit chain, granting access to user data without their knowledge.
How the Attack Works
DarkSword exploits several vulnerabilities, including zero-day ones, to bypass iOS security mechanisms and gain elevated system privileges.
Once compromised, attackers can:
- access messages, credentials, and files;
- track location;
- extract data from applications, including cryptocurrency wallets;
- execute remote code on the device.
The framework itself is not a single piece of malware—different groups have used their own modifications, tailoring tools for specific targets.
Threat to Users’ Crypto Assets
One of the key components of the package is Ghostblade. The main task of this module is to establish itself in the system after penetration and ensure full control over the device.
This tool establishes a connection with the attackers’ server and implements filtering and data collection, including account information from crypto applications and seed phrases.
Ghostblade takes actions to evade detection by security measures and can also download and execute additional modules, expanding the attack’s functionality.
CertiK specialists strongly recommend iOS device users take the following steps to safeguard their assets:
- update the OS to version 26.3;
- enable lockdown mode if the upgrade is not possible;
- check system account logins and remove any unknown ones;
- use hardware wallets and never store seed phrases on the phone.
Who is Behind the Attacks
According to researchers, DarkSword has been used by both commercial spyware providers and hacker groups presumably linked to governments.
Attacks have been recorded in several countries, including Ukraine, Turkey, and Middle Eastern states.
Experts noted that the emergence of DarkSword reflects a new trend: sophisticated hacking tools, once accessible only to state entities, are now spreading among a broader range of actors.
Back in March, the Ledger security team (Donjon) discovered a critical vulnerability in Android smartphones with MediaTek processors. The bug allows for the theft of cryptocurrency wallet keys within minutes.
Рассылки ForkLog: держите руку на пульсе биткоин-индустрии!


