
Prank trojan in Russia, European Commission data leak, and other cybersecurity news
This week in cybersecurity: a prankish trojan, C2 via Spotify, a $53m DEX hack, and an EU data breach.
Here are the week’s key cybersecurity developments.
- Spied, swapped crypto addresses and taunted victims: a prankish trojan found in Russia.
- C2 addresses for crypto-stealing malware found on Spotify and Chess.com.
- Hacker charged over $53m theft from the Uranium exchange.
- Researchers found an updated seed-phrase stealer for Apple and Android.
Spied, swapped crypto addresses and taunted victims: prank trojan uncovered in Russia
Researchers at Kaspersky Lab identified an active campaign in Russia spreading a new trojan. CrystalX is marketed under a CaaS model via ads on the social platforms Telegram and YouTube.
The software acts as both a spy and a stealer, enabling the following:
- steal browser credentials as well as Steam, Discord and Telegram accounts;
- silently replace crypto-wallet addresses in the clipboard;
- covertly record audio and video from the screen and webcam.
Its distinguishing feature is real-time mockery of the user. The panel includes a dedicated Rofl section with commands to:
- download an image from a specified URL and set it as the desktop background;
- rotate the display by 90°, 180° or 270°;
- shut down the OS via shutdown.exe;
- swap left- and right-mouse-button functions;
- turn off the monitor and lock input;
- make the cursor jitter at short intervals;
- hide all desktop icons and disable the taskbar, Task Manager and cmd.exe.
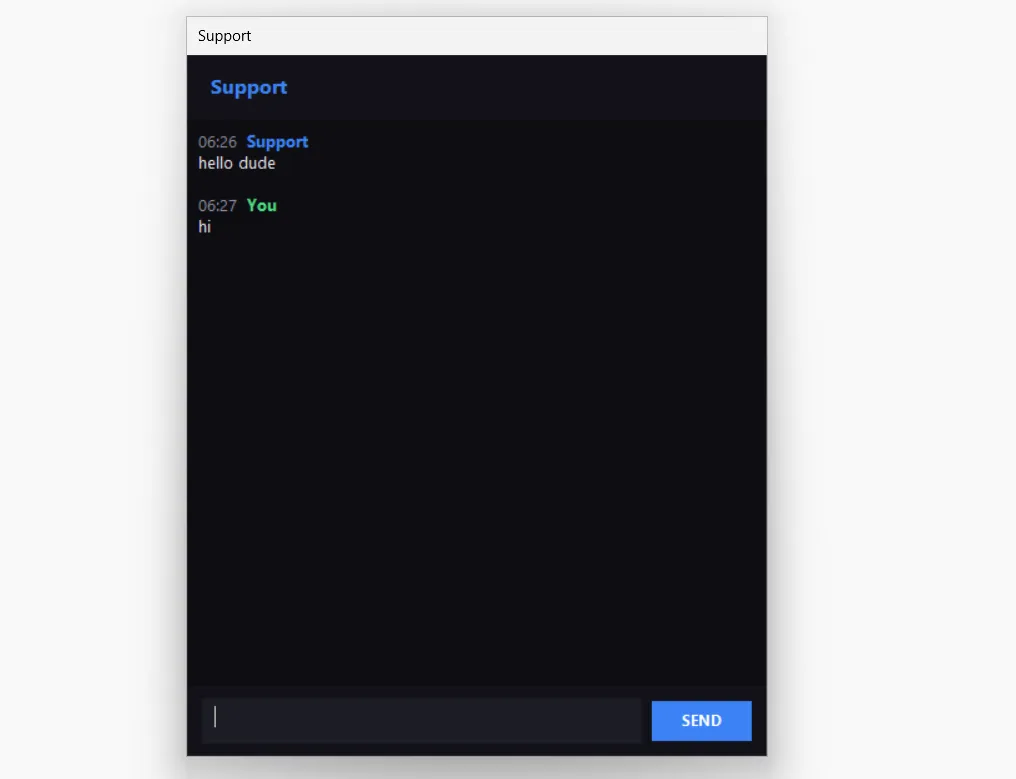
The attacker can also send a message to the victim, opening a dialog box for two-way chat.
As Leonid Bezvershenko, a senior Kaspersky GReAT expert, said in a comment to “Kod Durova”, the malware is under active development and support by its creators. He expects victim numbers to rise as the campaign’s geography widens.
Experts advise downloading apps only from official stores, installing a reputable antivirus, and enabling file-extension display in Windows to avoid accidentally launching .EXE, .VBS or .SCR files.
C2 addresses for crypto-stealing malware found on Spotify and Chess.com
Researchers at Solar 4RAYS found that hackers hide the controlling servers for the MaskGram stealer in Spotify and Chess.com profiles.
MaskGram targets the theft of accounts and cryptocurrencies and can fetch additional modules.
The malware collects data about the system, running processes and installed applications, and takes screenshots. It harvests information from Chromium-based browsers, crypto wallets, email clients, messengers and VPN apps.
Attackers distribute the software via social engineering, posing as cracked versions of paid tools for mass checking of logins and passwords against leaked databases, such as Netflix Hunter Combo Tool, Steam Combo Extractor and Deezer Checker.
According to experts, the malware uses the “dead drop” technique, or Dead Drop Resolver (DDR), which allows operators to store C2 information on public services and rotate it quickly.
An infected machine reaches out not to a suspicious IP but to Spotify or Chess.com, mimicking ordinary user activity.
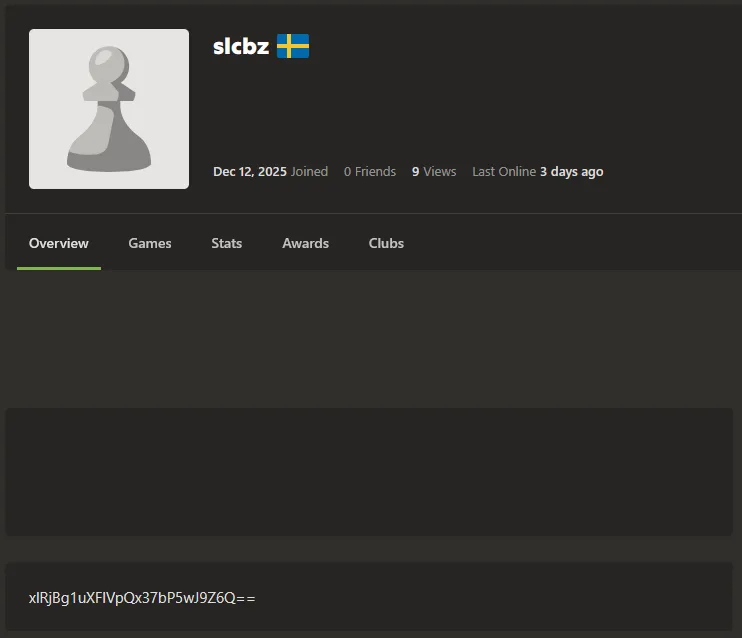
Each platform uses its own markers. For Chess.com, for example, it is the user profile’s about field. The extracted string is decoded into the server domain.
In March, Aikido specialists documented the use of the dead-drop technique by the GlassWorm stealer in crypto transactions on the Solana blockchain.
Hacker charged over $53m theft from Uranium crypto exchange
US prosecutors charged Jonathan Spalletta with stealing more than $53m from the Uranium Finance crypto exchange and laundering the proceeds.
In April 2021, Spalletta (also known as Cthulhon) hacked the BNB Chain-based Uranium decentralized exchange (DEX). The shortfall forced the company to shut down.
In February 2025, during a search, law enforcement seized valuables from the suspect’s home and restored access to cryptocurrency worth around $31m.
According to authorities, Spalletta laundered the stolen assets through DEXs and the mixer Tornado Cash. He spent the proceeds on collectibles:
- a Magic: The Gathering “Black Lotus” card — ~$500,000;
- 18 sealed Alpha Edition Magic: The Gathering boosters — ~$1.5m;
- a complete first-edition Pokémon base set — ~$750,000;
- an ancient Roman coin minted to commemorate the assassination of Julius Caesar — over $601,000.
He faces up to ten years in prison on computer-fraud charges and up to 20 years if convicted of money laundering.
Researchers find updated seed-phrase stealer targeting Apple and Android
Kaspersky Lab researchers found a new variant of the SparkCat cryptocurrency-stealing malware in the Apple App Store and Google Play Store, The Hacker News reports.
The stealer masquerades as innocuous apps such as corporate messengers and food-delivery services. In the background it scans victims’ photo galleries for crypto-wallet seed phrases.
Experts analyzed two tainted apps in the App Store and one in Google Play. They are aimed mainly at crypto users in Asia:
- iOS variant. Scans crypto-wallet mnemonic phrases in English. This approach makes the iOS version potentially more dangerous globally, as it can affect users regardless of region;
- Android variant. The updated version adds several layers of code obfuscation compared with earlier builds. It uses code virtualization and cross-platform programming languages to evade analysis. It also looks for keywords in Japanese, Korean and Chinese, underscoring a focus on Asia.
Experts believe a Chinese- or Russian-speaking operator is involved. The threat is actively evolving, and those behind it have strong technical skills.
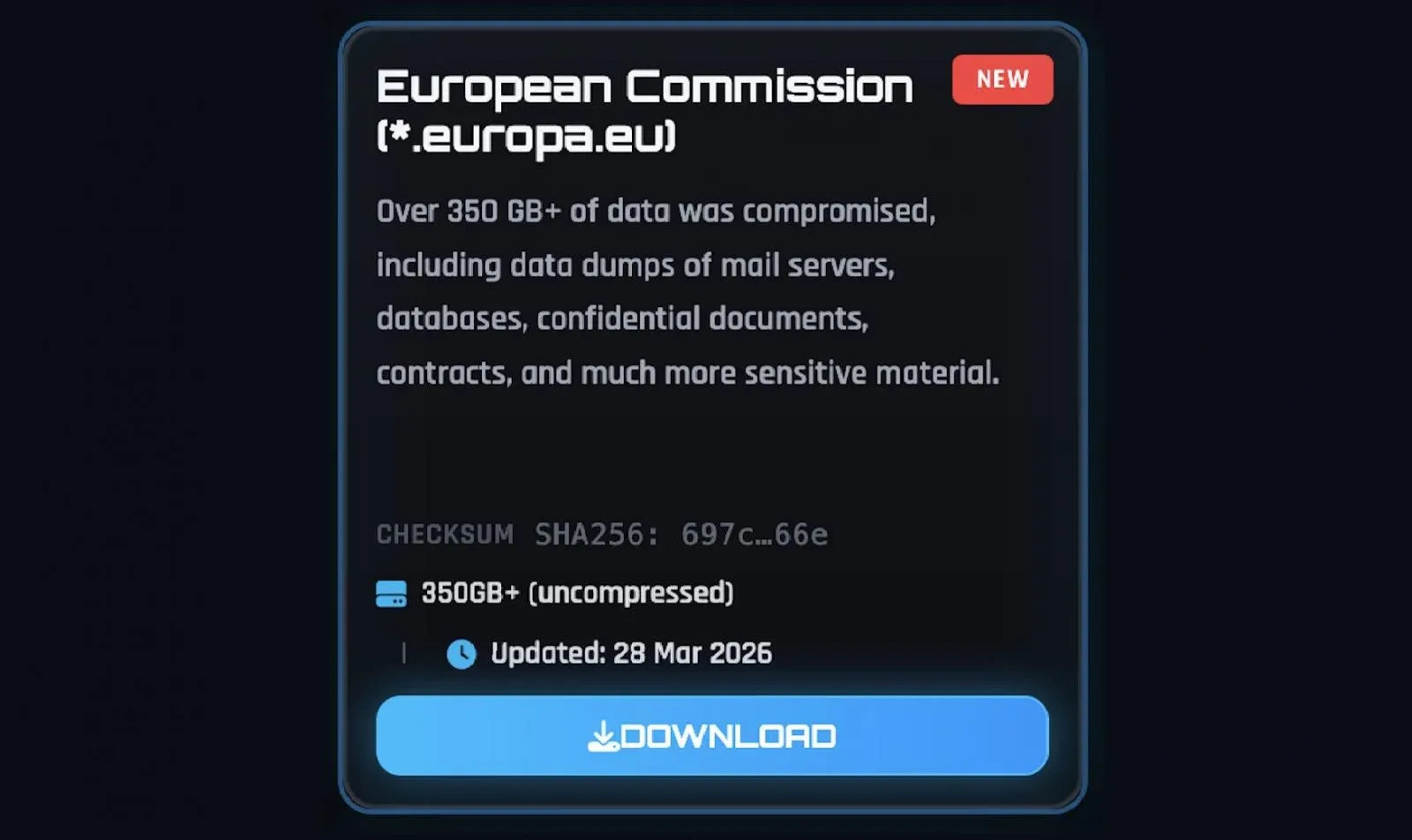
European Commission confirms data breach after ShinyHunters attack
The European Commission (EC) confirmed a data leak following a cyberattack on the Europa.eu web platform, for which the ShinyHunters extortionists claimed responsibility.
The EC said the incident did not disrupt the portal’s operations and was contained.
Although the Commission provided no details, the attackers told BleepingComputer they had stolen more than 350GB of data, including several databases. They did not reveal how they compromised AWS accounts but shared screenshots indicating access to some EC staff accounts.
The group also posted on its dark-web leak site, claiming more than 90GB of files were taken:
- mail-server dumps;
- databases;
- confidential documents and contracts;
- other sensitive materials.
Also on ForkLog:
What to read this weekend?
Drawing on research teams’ data, corporate reports and the state of play, ForkLog examines how brain–computer interface technologies are evolving.
Рассылки ForkLog: держите руку на пульсе биткоин-индустрии!


