
North Korean Agents Secretly Developed Code for Leading DeFi Projects for Seven Years
North Korean IT specialists have been integrating into DeFi projects for at least seven years.
For at least seven years, North Korean IT specialists have been integrating themselves into DeFi projects. This was stated by MetaMask developer Taylor Monahan.
Yuppppppp
Lots of DPRK IT Workers built the protocols you know and love, all the way back to defi summer
The “7 years blockchain dev experience” on their resume is not a lie. https://t.co/EQNgl5KhJ5
— Tay 💖 (@tayvano_) April 5, 2026
“Many IT workers have been building the protocols you know and love since the days of ‘DeFi summer’. The seven years of blockchain development experience on their resume is not a lie,” she wrote.
Among those affected by North Korean individuals, the expert highlighted SushiSwap, Thorchain, Fantom, Shib, Yearn, Floki, and many other projects.
Monahan’s comments were in response to a statement by Tim Ahl, founder of the Solana aggregator Titan. He recounted interviewing a candidate at a previous job who later turned out to be a member of the Lazarus Group.
“He was extremely skilled and always joined video calls. But when we invited him for an in-person meeting, he refused to fly over — we rejected his application. Later, his name appeared in a Lazarus leak. It turned out that the group now has agents not from North Korea who personally gain trust,” Ahl shared.
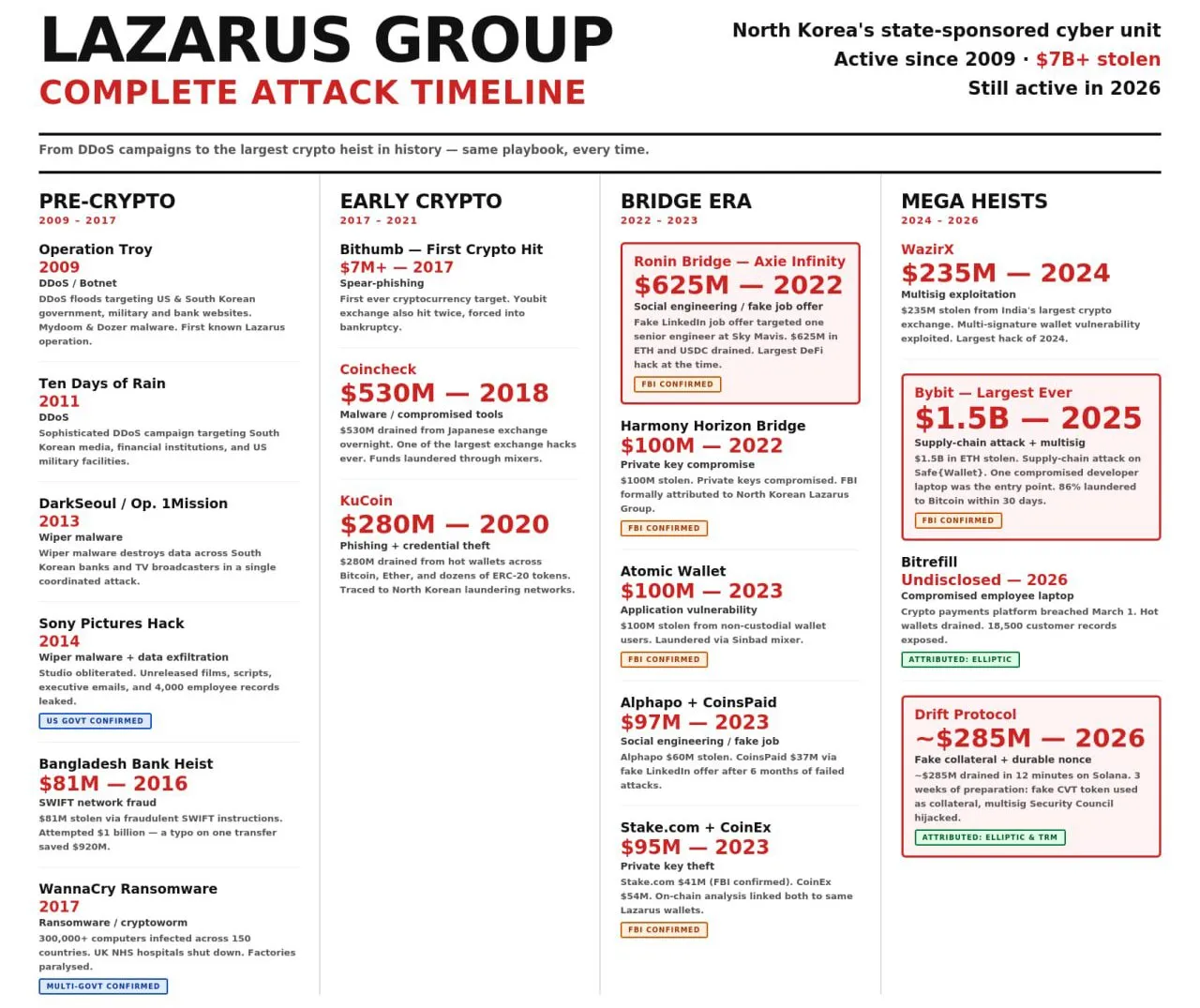
The discussions arose amid a report by the Drift Protocol team, which suffered a $280 million hack. The developers claimed that North Korean hackers were behind the attack.
Threat Assessment
Blockchain detective ZachXBT, who has repeatedly highlighted the threat posed by North Korea to the crypto industry, joined the discussion. According to him, Lazarus Group is a collective name for all “cyber actors supported by North Korea.”
Lazarus Group is the collective name for all DPRK state sponsored cyber actors.
The main issue is everyone groups them all together when the complexity of threats are different.
Threats via job postings, LinkedIn, email, Zoom, or interviews are basic and in no way… pic.twitter.com/NL8Jck5edN
— ZachXBT (@zachxbt) April 5, 2026
“The main problem is that everyone groups them all together, although the complexity of threats is different,” he noted.
The specialist described job postings, LinkedIn, emails, Zoom, and interviews as “simple and primitive” schemes. The main weapon of the perpetrators is persistence. According to him, today it is quite easy to identify a fraudster.
The only groups carrying out complex attacks remain TraderTraitor and AppleJeus.
Resources for Verification and Protection
The U.S. Treasury’s OFAC maintains a special website where crypto companies can check counterparties against current sanctions lists and receive warnings about typical fraud schemes by IT specialists.
Taylor Monahan has also created a knowledge base on GitHub, where one can find research-based information on North Korea’s activities in the digital asset sphere.
@tayvano_ has built a good resource on GitHub that’s a wealth of knowledge about DPRK using research collected from a variety of sources https://t.co/C9ZoSNVjIU
— ZachXBT (@zachxbt) April 5, 2026
Back in March, the Lazarus Group was suspected of attacking the cryptocurrency online store Bitrefill.
Рассылки ForkLog: держите руку на пульсе биткоин-индустрии!


